Applying Password Settings Objects On Windows Server 2012 R2
The Password Settings Objects (PSO) which was introduced in Windows Server 2008, apply a password policy for AD DS Fine-Grained Password and Account Lockout in Windows Server. When you configure the password policy from the Group policy for an Organizational Unit (OU), you can not apply the settings for other AD objects. So with password settings objects, you can do the task easily. I’m going to apply Password Settings Objects for the domain admin account in Windows Server 2012 R2.
Applying Password Settings Objects
In Windows Server 2012 R2 the PSO is applied through Active Directory Administrative Center.
1. So go to the Windows Server manager and open the Active directory administrative centre or type “DSAC” in the Run.
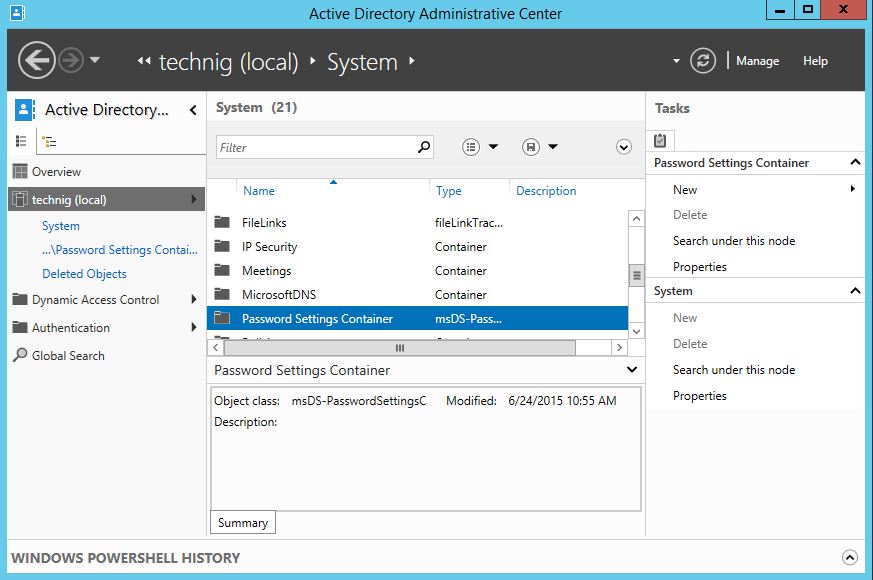
2. Select domain (Technig.local) then double click the System to open it. Then click the Password Settings Container to open it. See the above screenshot.
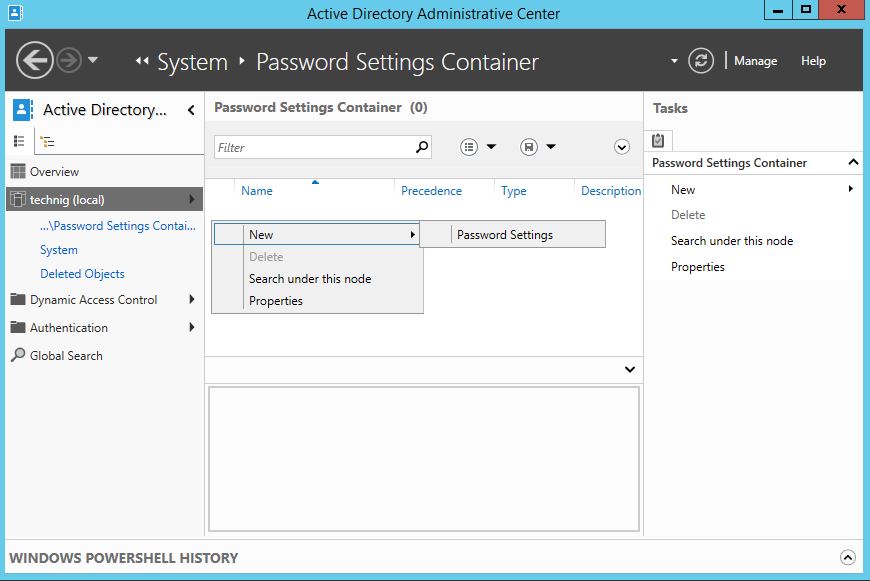
3. Right-click the main page of the password settings container and click New then click Password Settings.
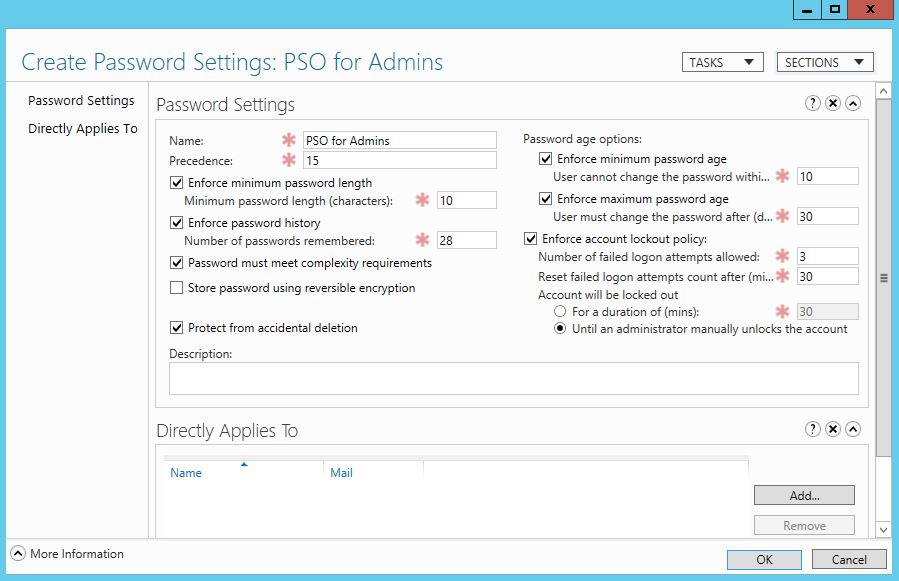
4. Configure the Password Settings whatever you want. Try to set the required options. If you are not familiar with the password settings policy, do the following.
Tick the checkboxes of:
- Enforce the minimum password length and enter the minimum password length =10.
- Enforce password history =28. It is the number of passwords remembered by a system that you can’t choose the password before the 28th time.
- Password must meet complexity requirements. The password must contain numbers, alphabets, symbols and etc.
- Protect from accidental deletion. The PSO will not delete accidentally.
- Enforce minimum password age and Enforce maximum password age. Bot shows the duration of password changes.
- Enforce account lockout policy. This will protect your account from unauthorized access or protect from brute-force attacks.
When all tasks are accomplished successfully, click OK to save the new Password Settings Objects.
5. Open the newly created password settings objects and click Directly Applies to, then add the groups you want to set and apply this PSO for them.
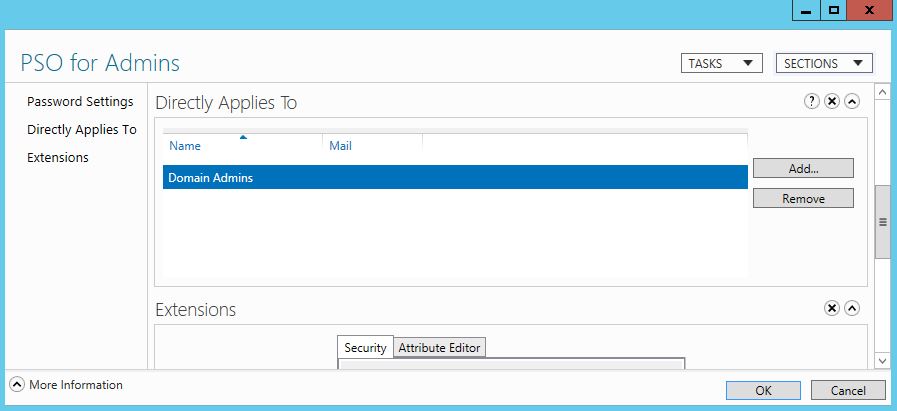
6. Close all pages and now try to test the PSO by changing the group members’ password or login attempts.
That’s all and any questions?
